Suspicions of academic dishonesty are on the rise, and traditional methods often fall short in uncovering the intricate web of digital deception. To effectively tackle this growing problem, institutions must turn to specialized expertise: ethical hackers. These skilled cybersecurity professionals possess the knowledge and tools to analyze online systems, identifying clues of cheating and providing actionable information. By employing an ethical hacker, you can guarantee the integrity of your academic environment and deter future instances of digital fraud.
- White hat specialists utilize advanced techniques to uncover hidden programs and track suspicious activity.
- Their investigations can reveal the scope of cheating, identifying those involved in fraudulent activities.
- Additionally, ethical hackers can suggest preventative measures to bolster your institution's cybersecurity posture and reduce future risks.
In today's digital age, it is imperative to remain vigilant against online deception. By hiring an ethical hacker, you can proactively tackle this threat, safeguarding the integrity of your institution and protecting its reputation.
Phone Taps & Text Trails: Exposing Infidelity with Discreet Monitoring
Suspicion got you down? wondering your partner's movements are hiding something untrustworthy? Finding out the truth about infidelity can be hard. But with discreet monitoring tools, you can gain valuable clues into their virtual life. Phone taps and text trails can expose the extent of deceit, giving you the power to make wise decisions about your relationship.
Begin with a proven monitoring service that offers advanced features like call recording and text message tracking. These tools allow you to listen conversations and read messages without raising any doubt. Remember, it's crucial to go ethically and legally when using such methods. Consult with a legal advisor to ensure you understand the consequences in your jurisdiction.
Gaining clarity into your partner's conduct can be a tough decision, but sometimes it's necessary for self-preservation and to make meaningful choices about your future.
Unmasking Social Media Lies
Dive deep into the shadowy world of social media with this eye-opening exposé. We're revealing hidden accounts, uncovering online deceit, and illuminating the strategies used by influencers. Learn how to identify fake profiles, analyze cryptic messages, and safeguard your privacy in the digital age. Get ready to penetrate the code of social media and take control.
- Expose the truth behind popular accounts
- Understand the hidden agendas of digital influencers
- Master the skills to survive in the chaotic world of social media
Thwart Cyber Trespassers: Secure Your Social Media with Expert Hacking Countermeasures
In the ever-evolving digital landscape, safeguarding your social media presence is paramount. Cyber trespassers are relentless in their attempts to penetrate accounts for malicious purposes. From identity theft to data exposure, the consequences can be devastating. To effectively combat these threats, it's crucial to implement robust security measures and cultivate a culture of online vigilance.
Implement strong passwords, activate two-factor authentication, and regularly review your privacy configurations. Stay informed about the latest security trends and best practices. Be wary of suspicious URLs, and never share sensitive information with untrusted sources. By proactively defending your social media accounts, you can minimize the risk of cyber trespass and enjoy a more secure online experience.
Discreet Phone Monitoring
In today's connected world, safety and security has become a paramount need. As our lives integrate more deeply with technology, it is crucial to ensure the well-being of ourselves and those we love most. Presenting a subtle solution: discreet phone monitoring. This innovative technology acts as a unseen guardian, offering invaluable insight into the digital lives of your children.
With advanced features, you can monitor calls. Acquire important information about their online activities, assisting you to guide your loved ones in the complex virtual realm.
Remember that overseeing responsibly is about peace of mind. It's a essential asset for guardians who desire toensure the safety of their family.
Exploring the Depths of Data: Digital Forensics and Hacking
In an era defined by digital connectivity, the line between the virtual and the real has become increasingly blurred. As our lives become more intertwined with technology, so too do the possibilities for both innovation and malicious activity. Digital forensics, a specialized field dedicated to uncovering the truth within digital evidence, has emerged as a crucial tool in navigating this complex landscape. darkweb hacker for hire Breached systems often leave behind a trail of clues – hidden files, deleted messages, and altered timestamps – that can provide invaluable insights into ,cyberattacks. Digital forensic investigators meticulously analyze these fragments of data, reconstructing the digital narrative to expose the perpetrators and bring them to justice.
- Specialized tools are employed to recover deleted files and extract hidden information from ,computer systems.
- ,Packet sniffing techniques help to trace the paths of malicious actors and identify their points of entry.
- Through careful analysis of the collected evidence, investigators can build a compelling case against cybercriminals, holding them accountable for their actions.
 Mason Gamble Then & Now!
Mason Gamble Then & Now! Andrea Barber Then & Now!
Andrea Barber Then & Now!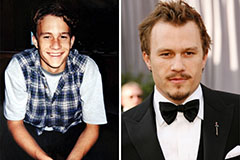 Heath Ledger Then & Now!
Heath Ledger Then & Now! Melissa Joan Hart Then & Now!
Melissa Joan Hart Then & Now! Rossy de Palma Then & Now!
Rossy de Palma Then & Now!